Awareness to Action: Building a More Resilient Community
The World Economic Forum’s identified ‘Cyber Inequity Crisis‘ – where 35% of small to mid-size organizations now report inadequate cyber resilience (a sevenfold increase since 2022) – by democratizing enterprise-grade cybersecurity that transforms vulnerable community businesses & non-profit organizations into resilient economic foundations capable of withstanding the systemic risks & compliance requirements that threaten entire supply chains and local economies.
%
CISOs Struggle with Regulatory Fragmentation
Professionals in LinkedIn Group
Average Recovery Cost (Microsoft Security 2004)
Potential Savings with Increase of Cyber Resilience
Join the Movement with
Our 5500+ Technologists, Governors, & Executives Community to Elevate Cognizance
The 5Cs Movement Principles:
Communication, Collaboration, Customization, Customer, Community
One Goal – Unify.
Our CyberRisk Governance System Unifies Cybersecurity, Compliance & Risk Management into an Holistic & Unbiased Cyber Risk Management Solution to Democratizes Enterprise-Grade Protection for Small, Non-Profit, & Mid-Size Organizations.
Our Vision
Elevate Cognizance
Hyper-Automate Resolution
Enabling Cyber-Resilience
What is CyberRisk Governance System?
Cyber risk governance refers to the strategic oversight and management framework that organizations use to identify, assess, and mitigate cybersecurity risks at the highest levels of leadership. It encompasses the policies, processes, and organizational structures that ensure cybersecurity risks are properly managed as part of overall business risk management.
North Star for Cyber Resilience
Our CyberRisk Governance (CRG) system transcends traditional IT boundaries by integrating NIST 8286 risk management methodology to systematically generate Risk Registers and Risk Profiles. This data-driven foundation enables our AI Governance research to develop Augmented Intelligence capabilities that generates compliance evidence throughout the resilience journey, delivering measurable outcomes in both cost efficiency and operational effectiveness.
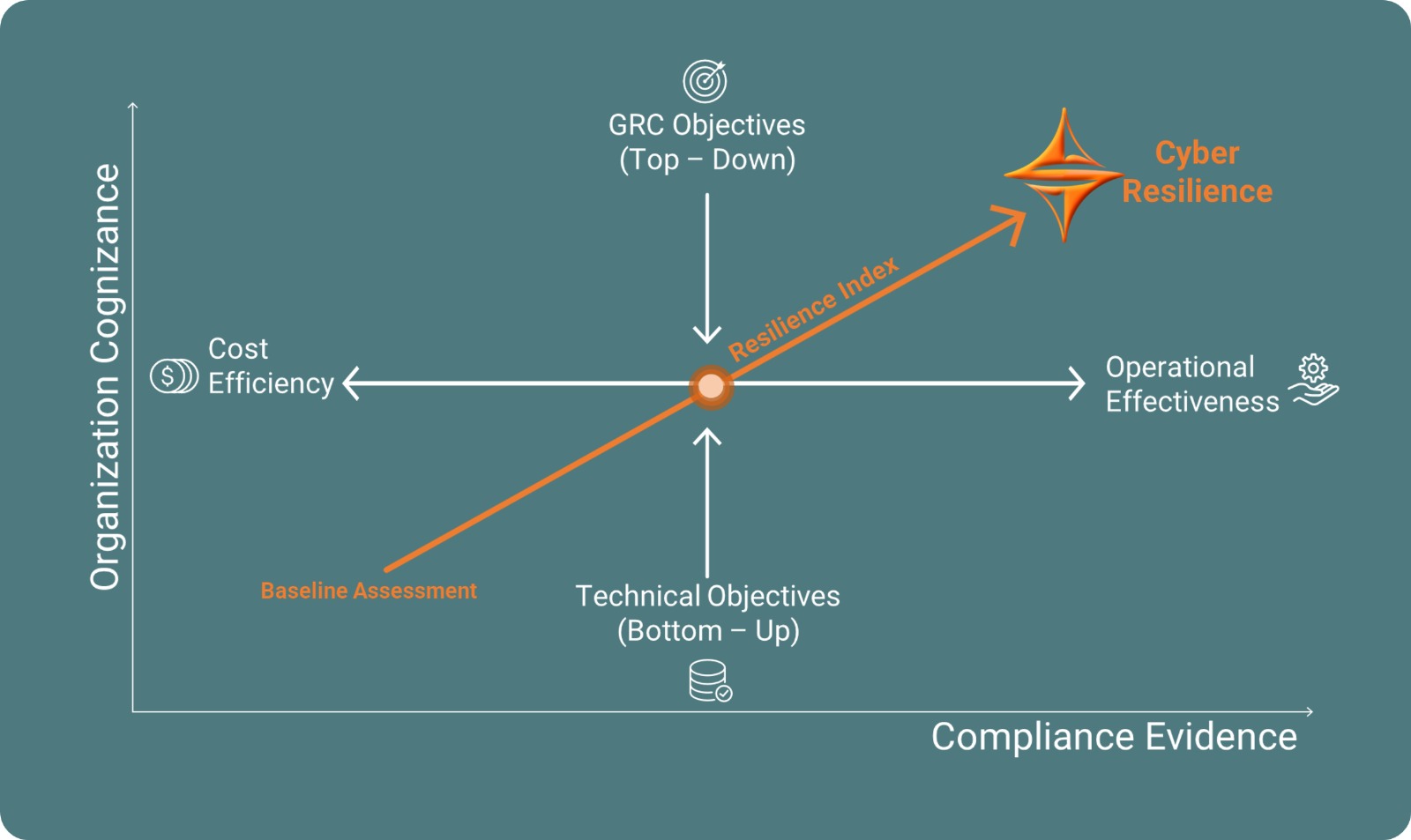
As part of our North Star to Cyber Resilience initiative to bridge cyber inequity gaps in risk management, we are developing our AI Governance Research Foundation to support our Hyper-Automate Resolution vision. This comprehensive approach reduces cost barriers by integrating open-source solutions, collaborating with educational institutions on real-world capstone projects, and leveraging our Cyber Risk Governance LinkedIn community’s subject matter expertise. Together, these elements contribute to our Global Resilience Index, enabling any organization to measure their cybersecurity maturity against peers within the same geographic area, compliance framework, and organizational size.
AI Governance Research Foundation
Our AI Governance Research Foundation transforms data analytics into intelligent action, accelerating Hyper-Automate Resolution through AI Square (Artificial & Augmented Intelligence) to eliminate cyber inequity gaps via strategic collaboration. By unifying open-source solutions, educational capstone projects, and our 5,000+ member Cyber Risk Governance community expertise, we are creating the Global Resilience Index—empowering organizations worldwide to benchmark cybersecurity maturity against geographic, compliance, and size-matched peers while accelerating their journey along the same North Star path to measurable cyber resilience.
Our platform integrates NIST 8286 to align cybersecurity and compliance through clear Risk Registers and Risk Profiles, preparing unbiased datasets for Agentic AI to power autonomous protection.
Risk Intelligence
Risk Prioritization Engine:
Business Metrics
Multi-Framework Alignment
The Resilience Revolution: Transforming Cyber Inequity Through Game-Changing Educational Alliances & Community Empowerment
Architecture Universal Cyber Immunity: From Local Communities to Global Enterprises
Our CyberRisk Governance ecosystem operates on four distinct compliance community levels, creating a comprehensive support network that addresses cyber resilience needs across Global, Regional, Local, and Industrial sectors to focus on our development of Cyber Resilience Index. Through strategic partnerships with educational institutes, we’ve developed an innovative approach that not only enhances cyber resilience for under-served communities but also provides real-world learning opportunities for the next generation of cyber risk management professionals.
The Four-Tier Compliance Community Framework:
At the Global level, we engage with multinational organizations navigating complex international regulatory frameworks and cross-border compliance requirements. Our Regional tier serves organizations operating within specific geographical areas, addressing regional regulatory standards and cultural cybersecurity considerations. The Local level encompasses community-based businesses, municipal organizations, and local government entities focusing on jurisdiction-specific compliance needs. Finally, our Industrial tier addresses sector-specific requirements across verticals such as healthcare, finance, manufacturing, hospitality, and critical infrastructure, each with unique layers of regulatory landscapes and threat profiles.
Educational Partnership Innovation:
Our collaboration with leading educational institutions creates a unique value proposition for small businesses and non-profit organizations who traditionally lack access to enterprise-grade cybersecurity expertise. Through carefully structured student-run capstone projects, we bridge the resource gap that often leaves these organizations vulnerable.
These partnerships work by matching cybersecurity students with real-world organizational challenges under the guidance of both academic advisors and our Subject Matter Experts. Students gain invaluable hands-on experience while small businesses and non-profits receive professional-grade security assessments, policy development, and implementation support at accessible price points.
Impact & Sustainability:
This ecosystem approach ensures that cyber resilience isn’t a privilege reserved for well-funded organizations. By leveraging the enthusiasm and fresh perspectives of students combined with seasoned expertise, we create sustainable pathways for comprehensive cybersecurity adoption across all organizational sizes and compliance levels.
Through capstone projects, future cyber risk management practitioners gain hands-on experience with industry-standard tools including our Unity Risk Indicator for Risk Register, Business Impact Analysis Playbook & Workbook for comprehensive risk evaluation, and Resilience-By-Design eBook for strategic implementation guidance. Students also access our extensive educational content through Cybersecurity Chronicles podcast, YouTube with Expert Insights and LinkedIn professional groups, ensuring they graduate with practical skills and real-world experience that directly translates to career readiness while strengthening the entire digital community’s defense posture from local communities to global enterprises.
Three Steps To C.A.R.E.
1
Know The Unknowns
You can’t protect what you can’t see—comprehensive asset discovery and vulnerability mapping transforms invisible risks into actionable intelligence with compliance prioritization.
2
Building Blocks
Transform fragmented security tools into an integrated defense ecosystem—where every component works in harmony with Subject Matter Experts to create unbreakable protection & resilient greater than the sum of its parts.
3
Measure & Monitor
Turn security into a data science—continuous measurement and intelligent monitoring transforms reactive incidents into proactive prevention, ensuring your defenses evolve faster than emerging threats.
C.A.R.E. – Simple, Holistic & Unbiased
A Clear, Powerful Path to Cyber Resilience
We combine the speed and scalability of AI with the precision of human expertise to deliver maximum operational effectiveness. Starts with our Unity Risk Indicator (Unity RI)— an open-source cyber risk visualization tool — integrates with cybersecurity solutions to create a customized, holistic dashboard. This enables real-time collaboration between internal and external teams, reducing bias from algorithmic influence and ensuring smarter, data-driven decisions for stronger cyber resilience.
Also built with comprehensive compliance in mind, we have incorporated 22 compliance frameworks into Unity RI to prioritize organizational compliance objectives, ensuring your cyber resilience strategy tethers with regulatory requirements, build compliance evidence, and comply industry best practices while maintaining operational excellence.
C
Comprehend
15–30 days
Initial assessment and data collection to understand your current risk landscape.
A
Act
Establishing policies and controls based on findings to build your defense foundation.
R
Review
Continuous monitoring, reporting, and adjustments to maintain resilience.
E
Evolve
Adaptive enhancement of your security posture as threats evolve.
Solutions for Every Stage of Your Journey
Resilience-By-Design eBook
Cyber Resilience Playbook
Business Impact Analysis Workbook
Score your risk and establish a clear register to prioritize.
RansomBloc
Automated protection for non-profits, schools, and small businesses.
SARA – Security Automation
AI-enhanced security automation with actionable insights.
Unity Risk Indicator
Open-source software for compliance clarity and centralized risk registers.
Proven Success Across Industries
Real results from real companies. See how our cybersecurity solutions have transformed organizations worldwide.
🏠
Manufacturing & Supply Chain
Defense compliance, security baseline via SARA, 82% reduction, ISO aligned
🛄
Financial
Services
IT compliance and posture assessment, clear gaps uncovered
🏥
Healthcare
External threats contained, sensitive IP protected
🏩
Hospitality
Global deployment of threat protection, high performance stats











